
Over 500,000 Zoom accounts are being sold on the dark web and hacker forums for less than a penny each, and in some cases, given away for free.
These credentials are gathered through credential stuffing attacks where threat actors attempt to login to Zoom using accounts leaked in older data breaches. The successful logins are then compiled into lists that are sold to other hackers.
Some of these Zoom accounts are offered for free on hacker forums so that hackers can use them in zoom-bombing pranks and malicious activities. Others are sold for less than a penny each.
Cybersecurity intelligence firm Cyble told BleepingComputer that around April 1st, 2020, they began to see free Zoom accounts being posted on hacker forums to gain an increased reputation in the hacker community.
These accounts are shared via text sharing sites where the threat actors are posting lists of email addresses and password combinations.
In the below example, 290 accounts related to colleges such as the University of Vermont, University of Colorado, Dartmouth, Lafayette, University of Florida, and many more were released for free.
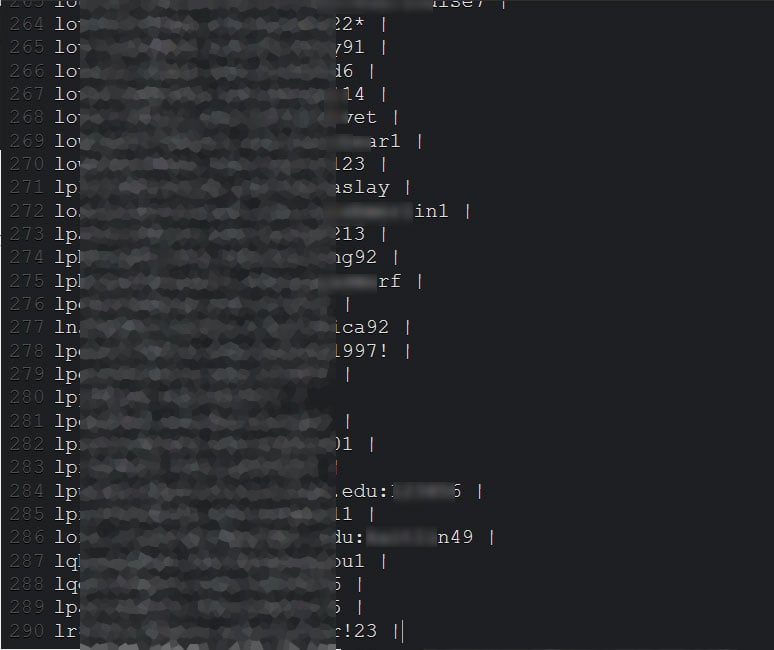
BleepingComputer has contacted random email addresses exposed in these lists and has confirmed that some of the credentials were correct.
One exposed user told BleepingComputer that the listed password was an old one, which indicates that some of these credentials are likely from older credential stuffing attacks.
Accounts sold in bulk
After seeing a seller posting accounts on a hacker forum, Cyble reached out to purchase a large number of accounts in bulk so that they could be used to warn their customers of the potential breach.
Cyble was able to purchase approximately 530,000 Zoom credentials for less than a penny each at $0.0020 per account.
The purchased accounts include a victim's email address, password, personal meeting URL, and their HostKey.

Cyble has told BleepingComputer that these accounts include ones for well-known companies such as Chase, Citibank, educational institutions, and more.
For the accounts that belonged to clients of Cyble, the intelligence firm was able to confirm that they were valid account credentials.
In a statement to BleepingComputer, Zoom stated that they have already hired intelligence firms to help find these password dumps so that they can reset affected users' passwords.
"It is common for web services that serve consumers to be targeted by this type of activity, which typically involves bad actors testing large numbers of already compromised credentials from other platforms to see if users have reused them elsewhere. This kind of attack generally does not affect our large enterprise customers that use their own single sign-on systems. We have already hired multiple intelligence firms to find these password dumps and the tools used to create them, as well as a firm that has shut down thousands of websites attempting to trick users into downloading malware or giving up their credentials. We continue to investigate, are locking accounts we have found to be compromised, asking users to change their passwords to something more secure, and are looking at implementing additional technology solutions to bolster our efforts.”
Change Zoom passwords if used elsewhere
As all companies are affected by credential stuffing attacks, you must use unique passwords for each site that you register an account.
With these attacks utilizing accounts exposed in past data breaches and then being sold online, using a unique password at every site will prevent a data breach from one site affecting you at a another site.
You can also check if your email address has been leaked in data breaches through the Have I Been Pwned and Cyble's AmIBreached data breach notification services.
Both services will list data breaches containing your email address and further confirm that your credentials have been potentially exposed.
Update 4/13/20: Made it clearer that credential stuffing attacks are not unique to Zoom. and added AmIBreached service from Cyble.
Update 4/14/20: Added Zoom's statement.


Comments
wetasol326 - 4 years ago
i'm happy i switched to jitsi meet before my zoom account got hacked, we use jitsi meet for our school work in bavaria
Math_Matters - 4 years ago
Headline: "Over 500,000 Zoom accounts sold on hacker forums, the dark web"
Lede: "Over 500 hundred thousand Zoom accounts are being sold on the dark web..."
So 500,000 or 50,000,000 (which is 500 x 100,000)? I'm guessing it's the former.
"Cyble was able to purchase over 530 thousand Zoom credentials for less than a penny each at .0020 cents per account."
530,000 x .0020 cents = 1060 cents = $10.60
0.0020 cents per account is indeed less than a penny each. It's exactly a penny per 500.
So all 500,000 accounts would be 1,000 pennies, or $10. And if it's actually 50 million accounts, it'd still be only $1000 for the whole enchilada.
In both cases you're off by two orders of magnitude.
Good info in the article aside from the numbers.
Moral of the story: don't mix numbers and words when using numbers. I made the same mistake in my comment and had to go back and edit it.
So 500,000 instead of 500 thousand (this is the one that tripped me up) and 530,000 instead of 530 thousand. "500 hundred thousand"--umm, WTF?
Lawrence Abrams - 4 years ago
Thanks and agreed. Fixed it in the article.
YazIT - 4 years ago
Either your math is off or the original headline you quoted was incorrect - unless the hacker was dumb enough and cheap enough to sell the data for $10.6
So, Is the per zoom account was priced at $0.002 or 0.002 of a cent?
If $0.002 then
In $: 530,000 x 0.002 = $1,060
In cents: 530,000 x 0.2 = 106,000 cents = 1,060 Dollars.
Otherwise, this is the worst data breach sell in history lol
Lawrence Abrams - 4 years ago
Yes, we already fixed our messed up lede :) "$: 530,000 x 0.002 = $1,060 " <= correct
Logica1 - 4 years ago
Zoom's comment ("It is common for web services that serve consumers to be targeted by this type of activity, which typically involves bad actors testing large numbers of already compromised credentials from other platforms [Credential Stuffing] to see if users have reused them elsewhere.") could be true in this case ONLY IF the sites from where the credentials were harvested also used the Zoom Meeting URL, Personal Meeting ID, and Host Code. But they don't. The fact that this cache includes all of those Zoom-specific details and not just the username and password, necessarily means that the data was obtained directly from Zoom (#hack) or by sniffing a whole lot of computers whose users had Zoom Host accounts (not that they just accessed a Zoom meeting at some point in their lives). There is more to this than what's on the surface....
jiniux - 4 years ago
Zoom Meeting URL, Personal Meeting ID and Host Code can be obtained by simply accessing to your Zoom account, and that's what attackers did. The problem is not Zoom itself; it is the huge amount of users who reuses the same password across the whole internet.
tchatch - 4 years ago
Hi.
SCAM ?
Lot of people start to wonder if this info is GENUINE.
Most of us are gravitating in dark web forums, but #NONE# has seen this leak.
Please, can you provide more information.
Thank you.
dataprivacyfines_com - 3 years ago
Will be interesting to see whether these breaches were reported, and whether data protection regulators would consider any fines for them. Just on the information we have, this could be an Article 32 (GDPR) case.